

Sophisticated threat and threat actors need better monitoring, preparation, responses, and capabilities. Attack vectors can steal your data and damage sensitive business assets. Threat management programs can enable the faster detection and response of such threats, preventing large scale data breaches and avoiding collateral damage.
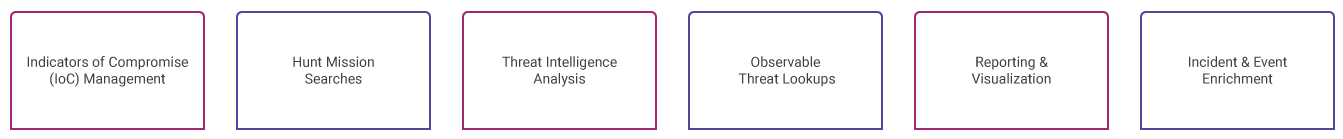
Threat Management service focus includes:
Aujas Threat Management Services can help you manage threats through vulnerability management frameworks and proactively identify known and unknown threats to predict, detect, and neutralize them in advance.
We also have innovated an automated threat hunting platform to gather context aware intelligence from external and internal sources to bolster your security defenses. The platform has Hadoop, Big Data & R as analytics tools to identify frauds, thefts, and data misuse.
Aujas Threat Management team can help you with:
|
Heuristic Approach
|
Feedback Loop Mechanism
|
|
Algorithm based pattern matching
|
We have five core competencies to address specific needs of threat mitigation. The objective is to transform your existing security posture through customized security services, enhancing detection speeds, hunt, and response times.
We realize every organization’s security needs are different, and an optimized security operations model is needed to drive threat management plans to manage potential security risks and meet compliance. Our team of experts can continuously monitor your security posture and protect your intellectual property, infrastructure, critical assets, and brand reputation.
Our resource capability brief:
Copyrights © 2025 All Rights Reserved by Aujas.